Related Articles
Rugged IIoT Environments, Handled: Soracom's Industrial-Grade SIM Card
Global provider of advanced IoT connectivity Soracom announced an industrial-grade SIM card for its portfolio of eSIM and IoT SIM solutions.
Read MoreIt's Time to Meet Digit: Agility Robotics Debuts a Human-Centric, Multi-Purpose Safety Robot
Digit is Agility Robotics' safe robot partner that multiplies productivities for human workforces.
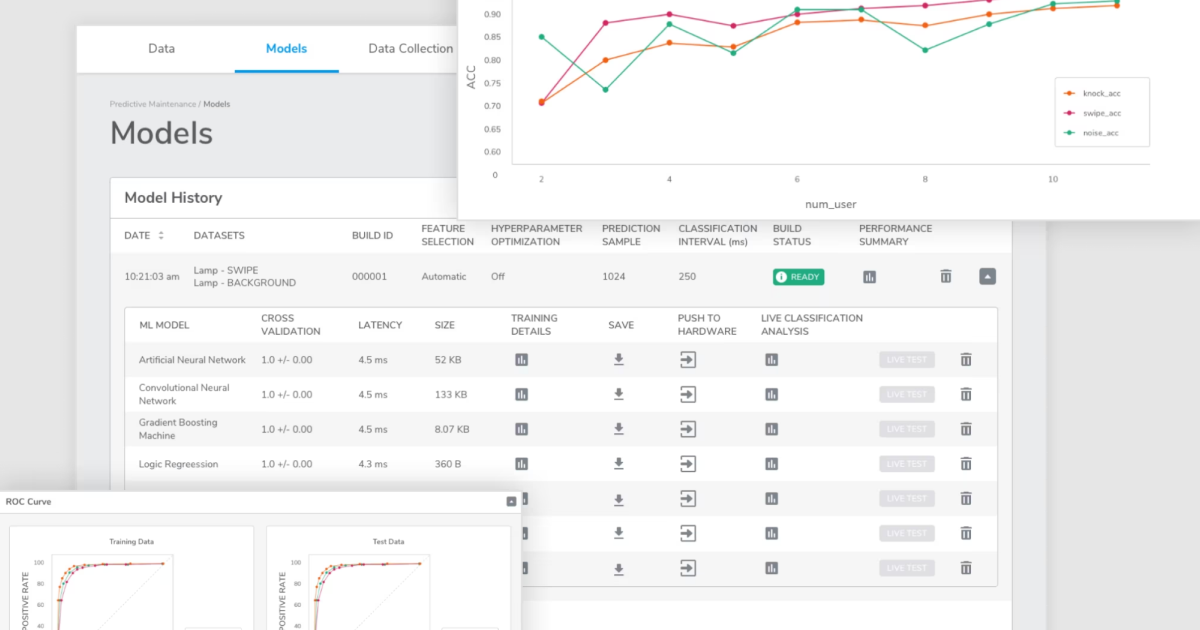
Read MoreTDK Announces Qeexo AutoML Platform Integration for Arm Keil MDK
TDK's new company Qeexo has launched its AutoML for Arm Keil MDK. This enables end-to-end embedded ML and development workflows.
Read MoreThe Next Wave of Computing: NVIDIA and Microsoft Collaborate on Powerful Enterprise Resources
Microsoft Azure will host NVIDIA Omniverse Cloud and NVIDIA DGX Cloud for supercharged enterprise solutions.
Read MoreThe Importance of Speed: An IoT Evolution Expo 2023 Discussion
Speed is crucial for distributed network success. At IoT Evolution Expo 2023 in Fort Lauderdale, FL, representatives from Internet of Things (IoT) sol…
Read More