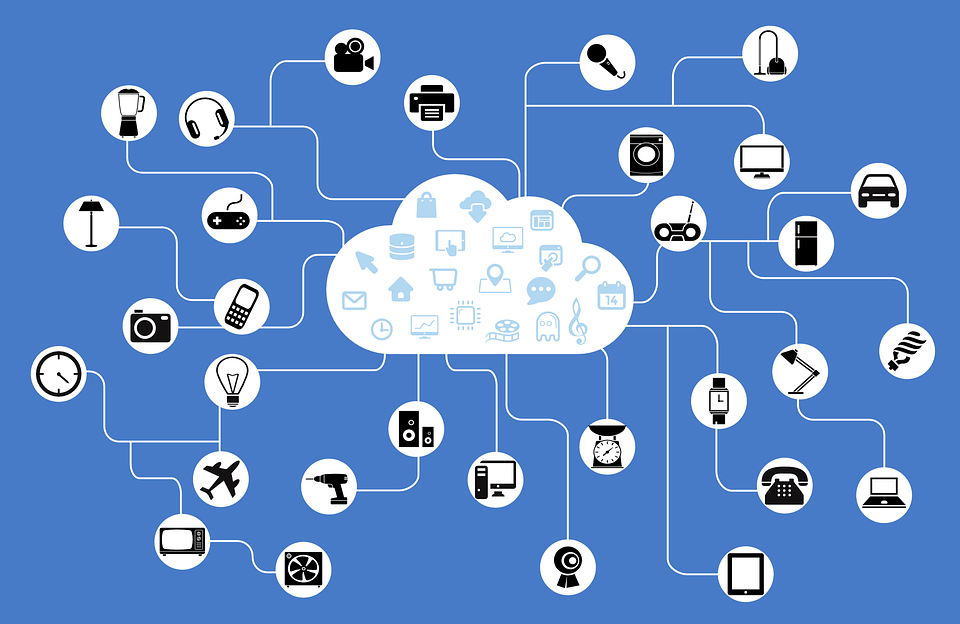
Experian is a leading global information services company and is now offering fraud prevention strategies to businesses and consumers looking to manage risk and increase security when using the IoT.
“The Internet of Things is only as strong as its weakest link, and it is important to fully understand what an interconnected environment means,” said Adam Fingersh, SVP and GM, fraud and identity business, Experian. “Opening products and services to the Internet dramatically increases the opportunities for cybercriminals, who can hack those products to get into your broader systems.”
As more “things” get connected, the usual laissez faire attitude to security just won’t cut it anymore. Recognizing that, Experian has issued the following 12 tips for consumers and business looking to stay safe.
Consumers
- Ensure that the products and services being purchased and connected are from reputable companies.
- Ensure that the providers of these products and services have clear privacy and data-usage policies.
- Be aware that data from any smart device may make its way to third parties for a variety of purposes and that there are not always standard policies across providers.
- Make sure that any access to these systems is always closely guarded.
- Be aware of the applications installed on devices and download applications only from reputable providers, such as the iTunes App Store or Google Play, rather than gray-market app platforms. Also, only download apps created by trusted entities.
Businesses
- Access to systems should require more than just credentials. Leverage cyber intelligence and complex device-recognition solutions to prevent unauthorized access.
- Designate who has access to systems and clarify why they need it. It is also important to understand the normal behavior of who is logging into these systems, so that when anomalies occur, immediate preventative action can be taken.
- Clearly outline roles and responsibilities in terms of access monitoring. This can be segmented by factors such as channel or line of business.
- Share intelligence across the consumer and enterprise side of your business.
- Partner with providers that have been successfully solving the account takeover problem. The concerns and vulnerabilities of Account Takeover problems in the digital realm using fit-for-purpose technologies are similar to the concerns and vulnerabilities in the Internet of Things world.
- Apply robust privacy policies and practices. Doing so will ensure that the data being collected is actually required for the services offered and that data-collection practices are easily understood by the consumer.
- Treat any collected data as highly sensitive information. It is important to note that even seemingly uninteresting data can be used by fraudsters to build robust and accurate stolen identities, which can be used for online impersonation, social engineering, phishing attacks and more.
Edited by
Peter Bernstein