In a stunning new report by Carbon Black, “Hacking, Escalating Attacks and The Role of Threat Hunting” the company revealed that 92 percent of UK companies surveyed have been breached in the last 12 months and almost half (44 percent) have been breached between three and five times.
In addition, Carbon Black (a leader in next-generation endpoint security) claimed also that 91 percent of those same businesses said attacks are becoming more sophisticated, “leveraging techniques such as: lateral movement, counter incident response, and island hopping.”
The report notes that spear phishing, ransomware, weak security processes, outdated software, commodity malware, crypto jacking, and supply chain attacks are all contributing to data breaches in the UK.
Perhaps the most dramatic data point shared by Carbon Black is that cybercriminals are currently spending approximately $1 trillion on developing cyberattack weapons, annually (according to the World Economic Forum), while the “defenders” (enterprises, governments, organizations) are spending about $96 billion (according to Gartner).
That’s a 10:1 ratio.
“The stats clearly show that defenders are not keeping up with attackers’ spending,” said Tom Kellermann, Chief Cybersecurity Officer, Carbon Black. “The fact that 92 percent of UK companies have experienced a breach in the last year and nearly half have been breached multiple times is sobering. It’s critical to educate UK businesses on the threats they face and how these threats can be mitigated.”
Carbon Black commissioned an independent research organization, Opinion Matters, to conduct the survey in August 2018. More than 250 UK CIOs, CTOs and CISOs were surveyed from companies from a range of vertical industries including financial, healthcare, government or local authority, retail, manufacturing, food and beverage, oil and gas, professional services, media and entertainment.
Rick McElroy, security strategist for Carbon Black, who has also held security positions with the U.S. Department of Defense, and in several industries including retail, insurance, entertainment, cloud computing, and higher education, is passionate about the need for technology companies in the security space to work together and continue to integrate more efficiently, including leveraging platforms and APIs.
“Education and innovation are the keys to improving the security landscape, as are ecosystems,” McElroy said. “No one company, technology or platform can solve for securing networks, clouds, applications and endpoints. Carbon Black is focused on leadership in the enterprise endpoint part of the overall security stack, as we believe this is where cybercriminals see the value. Just like us, cybercriminals go to work every day to write more code or tweak existing code as vulnerabilities are found and addressed so they can simply break in again and cause harm.”
Carbon Black supports a community of over 10,000 security professionals in Fortune 500 and other enterprises, governments and organizations around the world, who are increasingly helping each other as “threat hunters” as McElroy calls them.
“Cb Protection was the only solution to stop 100 percent of attacks in NSS Labs' 2017 Advanced Endpoint Protection (AEP) test,” according to the Carbon Black website, enabling the NSS Lab to lock down systems to stop malware, ransomware, zero-day, and non-malware attacks with built-in file-integrity monitoring, device control, and memory protection to block unauthorized changes.
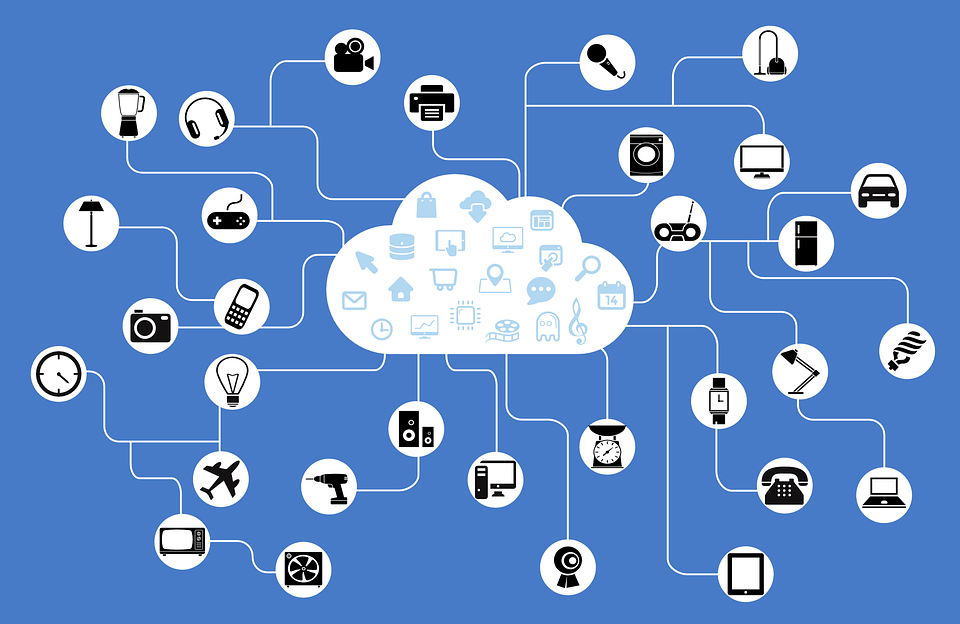
“We offer broad support for embedded, virtual and physical operating systems,” McElroy said, “and with the growth of the Internet of Things and a world where there will be increasingly more devices per human being than we could have imagined, focusing on the endpoints has been instrumental to our success. The more professionals who use our platform, the more participants we have, and data to analyze, all which can be harnessed to continually improve not only our platform, but how our platform works well with others.”
We reached out to security experts across a variety of other companies with specific solutions in their categories to get their reaction to Carbon Black’s latest report, to get a sense of what they are seeing in the market and developing in anticipation of the ever-expanding attack surface as more data is generated in more places traveling over more networks.
COGNIDA AND WINDMILL ENTERPRISE
Michael Hathaway, co-founder and CEO of Windmill Enterprise, the developer of the Cognida Platform weighed in saying “Risks of cyberattacks have increased in a large part due to an increasingly distributed enterprise data landscape. Data is spread across both public and private networks, each with their own unique security vulnerabilities. Corporate IT managers face a daunting task administering security and access policies across these diverse systems. It naturally follows that attacks are on the increase as there is an increasing quantity of systems that can be attacked.
The centralized identity management and access policy tools used in the past are hard pressed to address this evolving data landscape. A good first defense is to transition away from username/password authentication and transition to digital identities authenticated with public/private key cryptography. In addition, distributed ledger technology utilized by blockchain networks presents a powerful tool for addressing risks posed by these distributed systems. Blockchain technology serves as a distributed database where a consistent set of digital identities and security policies can be managed and distributed where they are needed. Windmill is committed to offering its customers a suite of open source tools to manage digital identities and enforce consistent security policies across network connected systems while taking advantage of a choice of existing and viable blockchain technologies
CENTRI TECHNOLOGIES
According to Don DeLoach of Centri, “It is clear the most predictable marker for a company taking serious steps to address their vulnerabilities is them being actually attacked. It’s like changing your diet after a heart attack, presuming you live. In an increasingly cyber-physical world, especially where the attack vectors are expanded with millions of small, low-powered devices that can increase these vulnerabilities, organizations need to stop thinking good enough is acceptable, and begin making layered, solid security a cornerstone of their overall architecture.”
DISPERSIVE TECHNOLOGIES
“Hackers launch attacks for different reasons. Some are bored. Some are motivated by ideology or financial gain. Some are sponsored by nation-states to conduct cyber espionage or disable critical infrastructure,” notes Rick Conklin, CTO of Dispersive Networks. “And, in an increasingly fast cycle that sees tools created by nation states available on the web at a fraction of their cost, even the least skilled hackers can launch sophisticated attacks.
It’s imperative that organizations follow a few basic rules to defend against the range of threats out there. Don’t talk to strangers. By that I mean use a call-out only paradigm that refuses connectivity to any but whitelisted sites. Implement a zero-trust perimeter that authenticates and authorizes devices before allowing them access to network services. Employ state-of-the-art techniques like our split-session multi-path techniques.
And finally, be creative in your security posture and recognize that hackers play by different rules.”
KRONTECH
Halis Osman Erkan, Chief Executive Officer of Krontech, said, “This report from Carbon Black is required reading for all CISOs and IT teams. Securing access to networks, clouds and applications is becoming more complex than ever, exacerbated by the growth of number of accounts, APIs, applications and endpoints and more. This is driven also by the rising adoption of connected solutions, including Internet of Things implementations for everything from asset tracking and management, to physical security and factory automation.
Securing corporate assets and keeping communications networks running in real time is made stronger through encryption and other techniques but managing keys and ensuring password strength can be time consuming and expensive for enterprises to manage by themselves, including the cost and other resources associated with hiring, training, managing and monitoring technicians and administrators.
Enterprises are increasingly leveraging solutions from suppliers they already trust, including CSPs providing network services to them. Given the rising threats and investments by cybercriminals, estimated at $1 trillion, there is a clear opportunity for service providers to expand their services by protecting against DDoS and encrypted attacks, protecting their customers from the subtle but high-risk attacks from inside the organization. Internal threats have risen to nearly half of all attacks, those orchestrated by employees or contractors with access to not only the network but to data and information, applications and services. Let’s fix this now.”
NEXT CURVE
Akshay Sharma, former Gartner analyst and neXt Curve's principal analyst commented expressly on the latest threats saying “Operators also need to clearly recognize the new category of security threat that is represented by Meltdown, Spectre and now Foreshadow. CISOs, CTOs and CIOs need to think of security holistically and consider new approaches to de-risk these processor-level threats. The C-Suite and the board need to understand the significant risks that processor-level vulnerabilities such as Foreshadow will have on their business and on their digital strategy.”
RIBBON COMMUNICATIONS
Kevin Riley, CTO of Ribbon Communications, commented on the rising threats against voice networks and real time communications applications. "While a great deal of attention has been placed on data security as part of cybercrime prevention, we're seeing more and more real time communications service providers investing in securing voice networks, particularly given that most voice calls are now data. Voice networks are vulnerable, including those which support contact centers, insurance companies, healthcare providers, financial services institutions, and other regulated industries.
As more and more voice travels over IP networks, as more voice activated technologies are adopted, and as more voice transcription services are contributing the databases of governments, enterprises and other organizations, the attack surface is growing. Additionally, without securing sessions through session border controllers and other SIP networking applications, there is a growing concern of pivot attacks, where bad actors identify open ports and other vulnerabilities to find a way into systems where massive databases contain private consumer data, sensitive enterprise data, and other high-value information.
These pivot attacks, while not yet broadly publicized for the obvious reasons, have also led to denial-of-service (DOS) and distributed-denial-of-service (DDOS) compromises, taking down entire networks, not just voice applications. Our customers understand this and are acting in advance to protect their own critical infrastructure, as well as their customers' services."
Edited by
Ken Briodagh